This is an old post. It may contain broken links and outdated information.

The last post on Openfire (discussing how to add SSL/TLS certificates) proved to be pretty popular, and I’ve gotten more than one request for a follow-on about securing Openfire clients—that is, forcing them to communicate with the Openfire server using only an ecrypted SSL/TLS connection rather than cleartext. In this post we’ll go through how to configure three popular IM applications to use SSL/TLS with Openfire. I’ll also add notes about how to enable OTR messaging encryption on two of those IM clients.
TLS encryption with Adium

I use OS X for day-to-day computing because I want the flexibility of a BSD-based operating system coupled with ease of use, and because I like it better than Windows. The most popular instant messaging client for OS X is easily Adium, a GPL client based on the libpurple protocol library, which also powers the multi-platform Pidgin (more on that client in the next section). Adium works on just about every IM network known to man, but its XMPP support is why we’re focusing on it here.
Start Adium and log on to your Openfire server, then click Adium > Preferences in the menubar. On the Accounts tab, click on your account and then click the Edit button. Navigate to the Options tab, which looks like this:
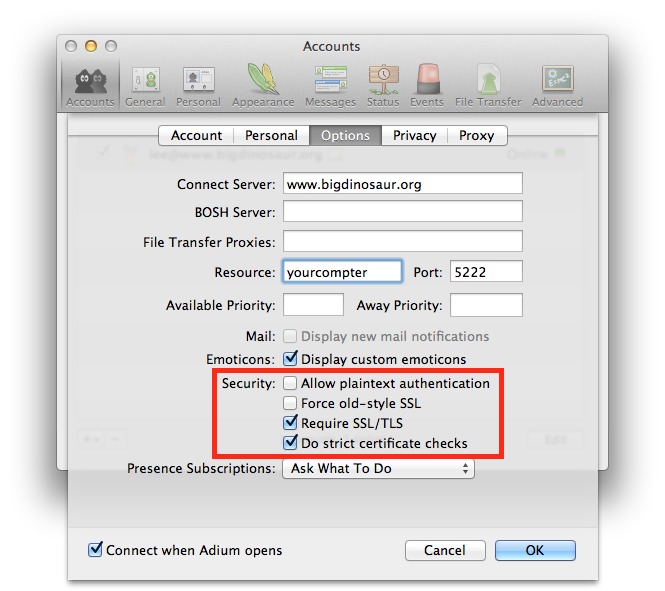
Look at the Security section, highlighted in red in the image above, and make sure the options are set as indicated. You want plaintext authentication disallowed, old-style SSL disallowed, SSL/TLS required, and strict certificate checks enabled.
The second option, about forcing “old-style SSL”, is worth mentioning in a bit more detail. Though we often use the acronyms “SSL” and “TLS” interchangably, it’s important to remember that TLS (Transport Layer Security) is a newer and more secure protocol than old-style SSL. This “Force old-style SSL” option is there for compatibility’s sake; Openfire supports the newer TLS protocol and you should use it.
OTR encryption with Adium
OTR Messaging (where OTR == “Off-The-Record”) is an add-on for instant messaging clients that securely encrypts not just the messaging between clients and servers, but also between clients and other clients. This handy thing to have Openfire and other IM servers have the ability to monitor and log the contents of instant messages between their connected clients. The monitoring and logging functionality exists for legitimate reasons (for example, to verify that business IM users aren’t sending PII or proprietary information through the IM system), but from the end user’s perspective such scrutiny isn’t always necessary or welcome. Some instant message traffic is sensitive in nature and should only be sent encrypted.
Some IM clients only support OTR encryption via an installable add-on; fortunately, Adium comes with OTR support already built-in. The configuration options for it are located in the Privacy tab under your account’s properties:
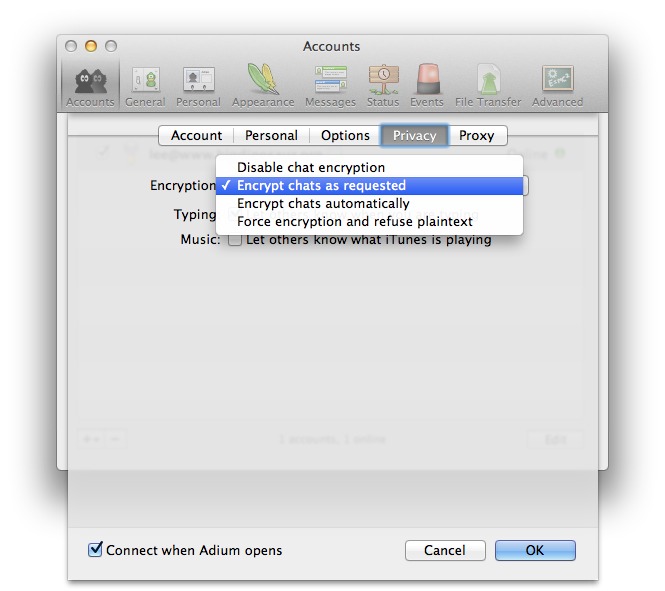
You can have Adium use no encryption at all, start chats unencrypted and encrypt if either client requests, start encrypted automatically if the other client supports encryption, or always encrypt and refuse all unencrypted chats.
TLS encryption with Pidgin

Windows and GNU/Linux users who need a multi-network IM client have several choices. Trillian remains a popular favorite, in spite of how bad it is, but we’re going to focus on Pidgin, which is based around the same messaging library as OS X’s Adium and which won’t extort cash out of you for the privilege of sending advertising-free IMs, unlike Trillian and their despicable “Pro” upselling. If you’re a Trillian user, do yourself a favor and abandon that garbage in favor of superior free (as in beer and speech) software.
To ensure Pidgin is only using TLS to communicate with Openfire, start it up and press ctrl-a to invoke the Manage Accounts window, and then highlight your XMPP account and click Modify. Then, in the Modify Accounts window, click on the Advanced tab:
Ensure that the “Connection Security” drop-down is set to “Require Encryption” and that the “Allow plaintext auth…” box is unchecked, and then click “Save” to apply your choices.
OTR encryption with Pidgin
Unlike Adium, Pidgin doesn’t come with OTR Messaging support right out of the box, but it can be added with a quick download. A link to the Win32 installer is located right on the main OTR project page; Ubuntu and Debian users have it even easier, as there is a prebuilt OTR plug-in in the repositories that can be installed with sudo aptitude install pidgin-otr.
Once the OTR messaging plug-in is installed, you’ll need to enable it. Press ctrl-u to invoke the Pidgin plugins menu, and make sure “Off-the-Record Messaging” is checked:
Then, highlight it and click the Configure Plugin button:
You don’t need to generate a private key, as the system will do that for you the first time you initiate an encrypted chat (though you can generate one now if you really want). The other options here can be set to taste, but make sure to at least check “Enable private messaging”. You can also check “Automatically initiate private messaging” to have Pidgin attempt to start all chats encrypted, and “Require private messaging” to cause Pidgin to reject all non-encrypted communication.
TLS encryption with Digsby

Digsby is another free multi-service IM client, with some additional social networking features which makes it attractive for people who value that sort of thing. Enough folks I know use it that I wanted to include it in here, although Digsby’s biggest failing is that as of today it still doesn’t support OTR Messaging or any other client-to-client encryption method, which means that your messages are readable by the IM server administrator. Most folks don’t really care, but it’s one of those features where when you need it, you really need it.
To get Digsby to only use TLS when it communicates with Openfire, sign in and go Tools > (Your Account Name) > Edit Account, and then click the Advanced disclosure widget in the account window to expose the properties we want to modify:
Ensure “Require TLS” is selected, and uncheck “Allow Plaintext Login” to force Digsby to always use TLS and only TLS.
Testing OTR encryption
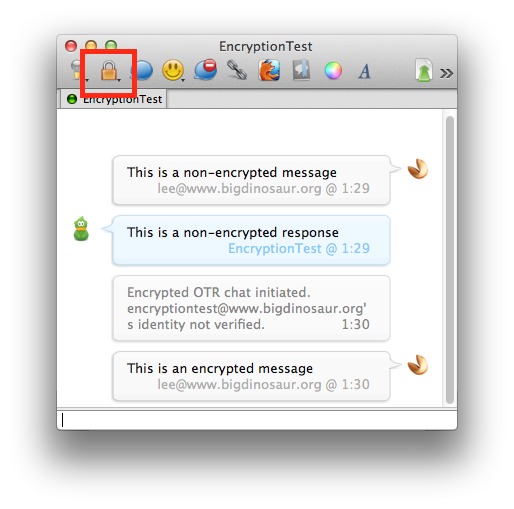
For clients with OTR Messaging enabled, you should perform a test converstation to ensure that encryption is functioning correctly. In the screenshot below (taken from Pidgin because it’s a bit more vocal about what’s going on) I’ve started a non-encrypted chat, then sent an encryption request, exchanged keys, and verified the key fingerprints.
The encrypted session was invoked by pressing the OTR button (highlighted with the red box), which changes state depending on the encryption state of the conversation. It will say “Not Private” if the chat is unencrypted, “Unverified” if the chat is encrypted but you’ve not yet verified the identity of the person with whom you’re speaking, and “Private” (as in the screenshot) if you’ve positively identified your chat partner.
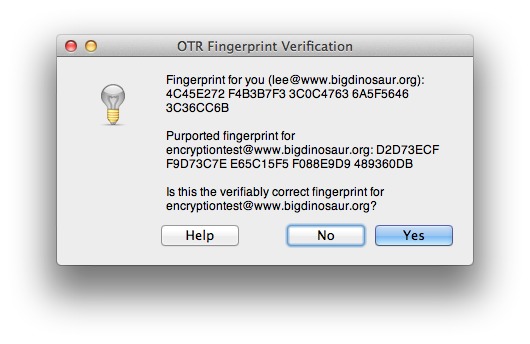
Identification is typically done by key fingerprint verification. There are lots of places to read about how public key fingerprints work, so I won’t rehash them in depth here, except to say that it’s always best to verify the public key fingerprint of the person with whom you’re chatting by using an out-of-band method—for example, the very first time you’re going to have an encrypted chat with someone, call them on the phone and have them read off their public key fingerprint, and you read off yours. When you begin the chat, your IM client will ask you to validate their key fingerprint in order to ensure that the person with whom you’re chatting is actually for-real the person you believe them to be:
All this verification stuff serves a vital purpose. Recall that encryption is only half of true secure communication; the other half is identity verification. What good does it do to be able to encrypt communications to another person if you can’t be sure that you’re actually talking to that person in the first place? Public key fingerprint verification, therefore, is one method to help ensure that you’re actually chatting with the right person.
The process is much the same on Adium, with the encrypted chat initated by clicking the lock icon in the window’s toolbar (highlighted in red below):
The key fingerprint verification must occur on this end as well, so that both endpoints verify each others’ identities:
And that’s it. I’m a fan of the notion that everything should be encrypted whenever possible, and so I tend to leave my clients set to automatically encrypt; however, some folks on the Bigdinosaur.org IM server use clients that don’t support OTR Messaging, so I don’t set Adium to automatically reject all plaintext communication.
Still, every client out there should support TLS-encrypted communication between XMPP clients and an Openfire or other XMPP server, and there’s no reason I can think of why those options shouldn’t be enabled.